Microsoft Entra ID, formerly known as Azure Active Directory (Azure AD), is a cloud-based identity and access management (IAM) service from Microsoft. It helps organizations secure and manage identities, enabling users to access both cloud and on-premises resources. Essentially, it provides a centralized way to manage user accounts, permissions, and access to various applications and services.
Configure Microsoft Entra ID SSO for Profit.co
Here’s how to integrate Profit.co with Microsoft Entra ID so that your users can automatically sign in to Profit.co using their Microsoft Entra ID accounts.
Step 1
Login to Microsoft Entra ID portal and access the Microsoft Entra ID

Step 2
Click on Enterprise Applications from the manage navigation

Step 3
Search for Profit.co and select the application.

Note: If you don’t find it there, kindly click on “New Application” and search to add it to your account.
After selecting the application click on Create

Step 4
Select Single Sign-on in the left menu and select ’SAML’

Click on the Edit button and click on Save


Step 5
After saving, scroll down a bit and download the Federation Metadata XML in the SAML certificates.

Step 6
Now select Users and groups in the left menu, and click “Add user” to assign the app to the users.



Navigate to Settings from the left navigation panel.
Click on Integrations, On the Connectors page, Select the SAML SSO tab and click on the Microsoft Entra ID Authorize button.

Click on Authorize Microsoft Entra ID and paste the Issuer ID and X509 certificate, then click the Authorize button.

Step 7
Once the app is assigned, the users can find the Profit.co under My Apps. Clicking on the app would take them to their Profit.co account.

Reference
https://docs.microsoft.com/bs-cyrl-ba/azure/active-directory/manage-apps/add-gallery-app
Configure Microsoft Entra ID SSO and User Provisioning using custom app creation
Step 1
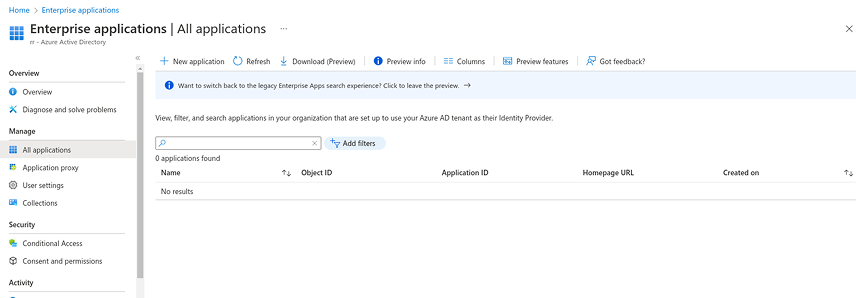
Navigate to the Microsoft Entra ID Portal Home Page and click on Enterprise Applications.

Step 2
Click on the New Application button.
Step 3
To start creating your own application, click the button. Name the application (for example, Profit.co OKR Software), choose Integrate any other application (Non-gallery), and then click the “Create” button.


Step 4
Following the creation of the application, the Application Detail page will be displayed as shown below, and under Single sign-on and Provisioning options on the left menu, we must enter the Profit.co SSO and SCIM Configuration Details.

Step 5
Navigate to Single sign-on -> SAML and enter the following details. Click on the Edit button of the Basic SAML Configuration Section.
Click on Add identifier and provide
US Region –

(or)
EU Region –

Click on Add reply URL and provide
US Region –

(or)
EU Region –




Step 6
Navigate to the Users and groups option in the left menu and click on Add user/group to add the required users and groups to the app.

Step 7
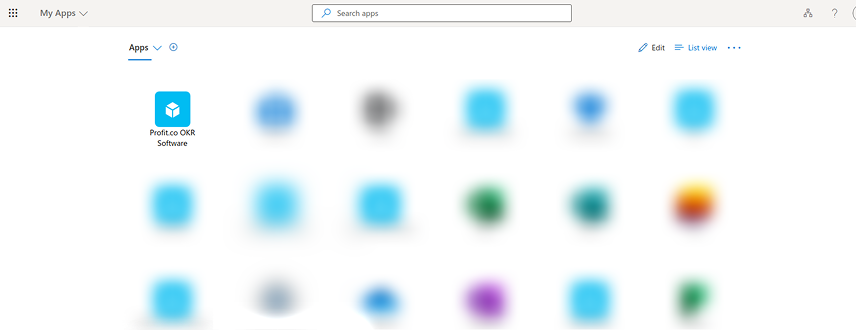
Got to https://myapplications.microsoft.com/. The assigned app (Profit.co OKR Software) will be listed here. Clicking on the App will redirect to the user’s Profit.co Account.
Step 8
Navigate to the Provisioning option in the left menu and click on the Get started button.

Step 9
Choose Automatic under Provisioning Mode and enter the following information.
Tenant URL
Either
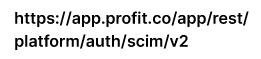
(or)
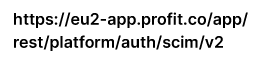
based on the region of your Profit.co Application.
Secret Token
To generate the secret token in Profit.co, go to Settings → Security → API Access and get the values of API Key and SCIM Key.
Form the Secret Token in the following format and provide it in the Secret Token field.
[API_KEY]:[SCIM_KEY]
To verify the SCIM connection, click the Test Connection button. When the validation is successful, click the Save button in the top left corner.

Step 10
Navigate to the Provisioning option again and click on the Start Provisioning button.

Step 11
Profit.co will create a user each time a user is assigned to this application. A user’s access to profit.co will be suspended if they are uninstalled from the App.
Profit.co will update every 45 minutes with the latest information.
The supported attributes are as follows,
- First name
- Last name
- Email address
- Active status
- JobTitle
- Department
- Managers
Note:
1. If a department already exists in Profit.co in either an enabled or disabled state, it will be merged. No duplicate departments will be created. The user sync to the department won’t take place if the department is disabled.
2. The department will be created as a new department if it does not already exist in Profit.co.
How do I disable the department and job title mapping fields?
In Microsoft Entra ID SSO Click on Edit attribute mappings under Manage User Provisioning and select the Provision Microsoft Entra ID users


Remove the job title and department attribute from the attribute mapping, and then click Save.
