Duo is an identity management service which eliminates username and password struggle. Duo authenticates your users using existing on-premises or cloud-based directory credentials and prompts for two-factor authentication before permitting access. Single sign-on (SSO) from Duo provides users with an easy and consistent login experience for any and every application, whether it’s on-premises or cloud-based.
How do you enable SAML Authentication for Profit.co within DUO?
Here’s a walk-through of setting up Cisco-DUO as your SAML Identity Provider for Profit.co.
Step 1:
Log in to your Duo account as an admin or register with Duo with the URL https://admin.duosecurity.com/
Step 2:
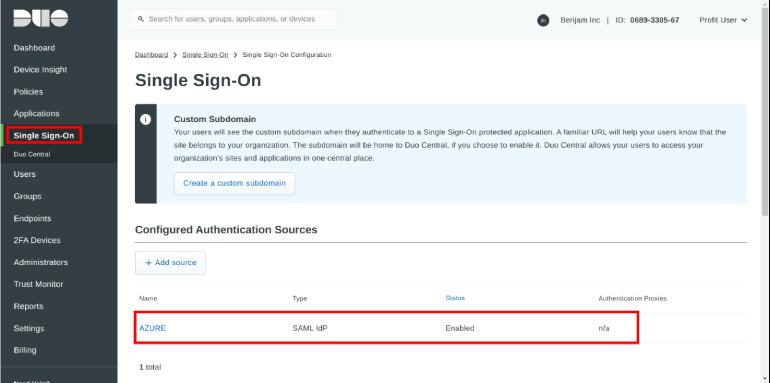
Log in to your dashboard and select the Single Sign On tab and also verify on Idp Authentication Source with Duo Central.
Step 3:
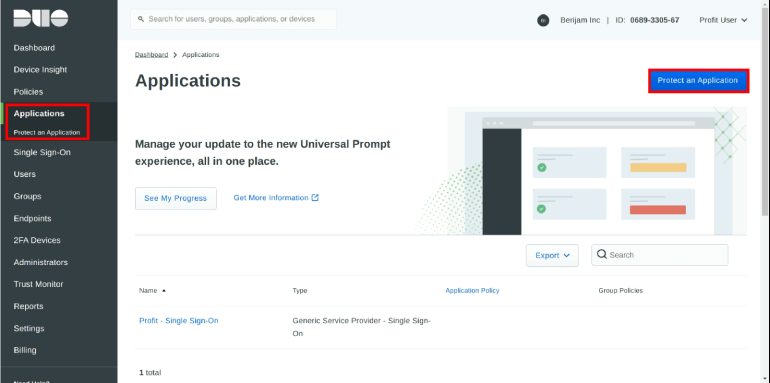
Navigate to the Applications Tab, click on the Protect an application button in Protect application Tab.
Step 4:
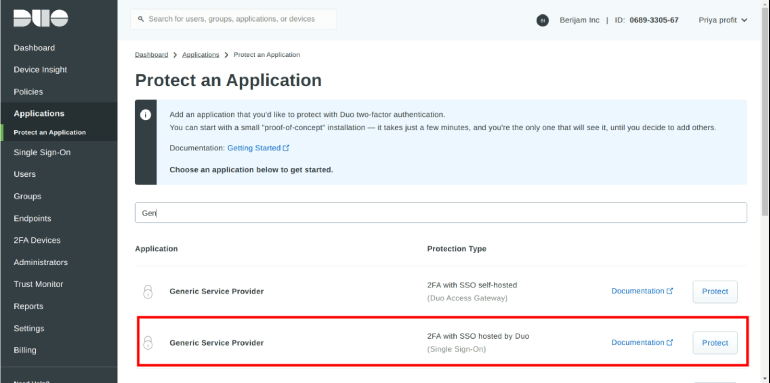
Search and Select the Generic Service Provider with a protection type of “2FA with SSO hosted by Duo (Single Sign-On)” in the applications list.
Step 5:
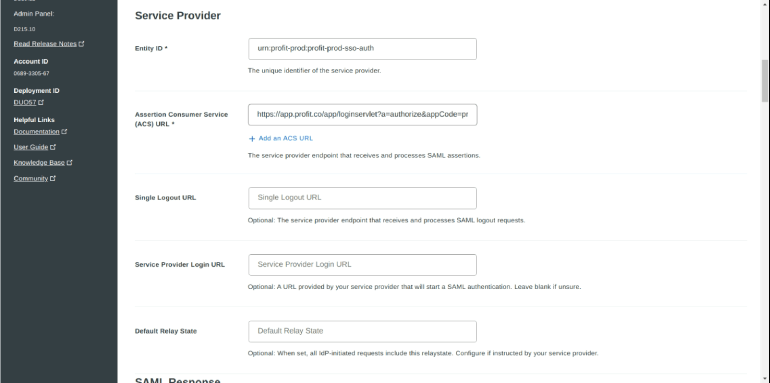
Enter the information provided by Profit.co application into the Service Provider section:
| Entity ID | urn:profit-prod:profit-prod-sso-auth |
|---|---|
| Assertion Consumer Service (ACS) URL | https://app.profit.co/app/loginservlet?a=authorize&appCode=profit&integrationCode=CISCO_DUO |
Step 6:
Enter the information provided by Profit.co application into the SAML Response section.
| NameID format | urn:oasis:names:tc:SAML:1.1:nameid-format:emailaddress | ||||
|---|---|---|---|---|---|
| NameID Attribute | <Email Address> as G Suite AuthN Source(or) <Username> as Azure AD AuthN Source | ||||
| Signature Algorithm | SHA-256 | ||||
| ACS URL |
US region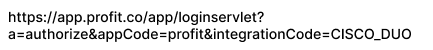 (or)EU region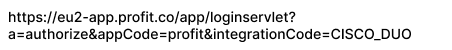 |
||||
| Signing Options | Sign assertion | ||||
| Map Attributes |
| ||||
| Create Attributes |
|

Step 7:
Enter the Name in Profit.co-Single Sign On under the Settings section and click to Save.
Step 8:
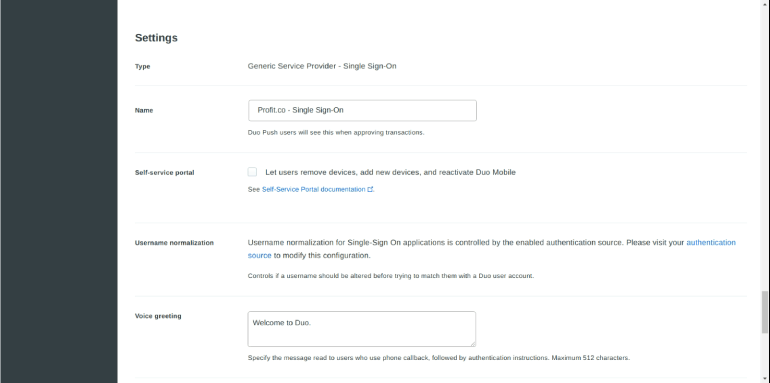
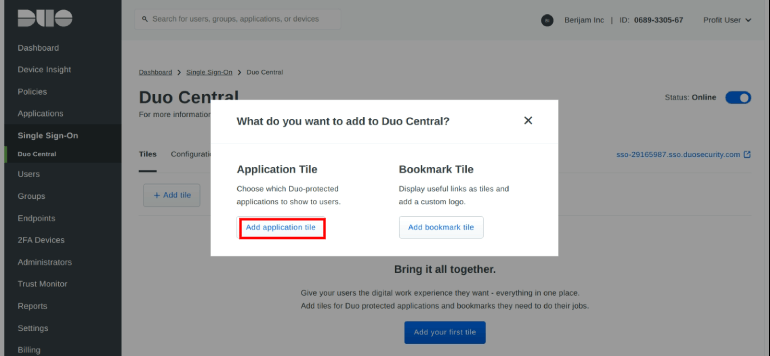
Navigate to the Duo Central Tab and click on the Add Tile button.
Step 9:
In the Add Tile page, Select the Add application Tile
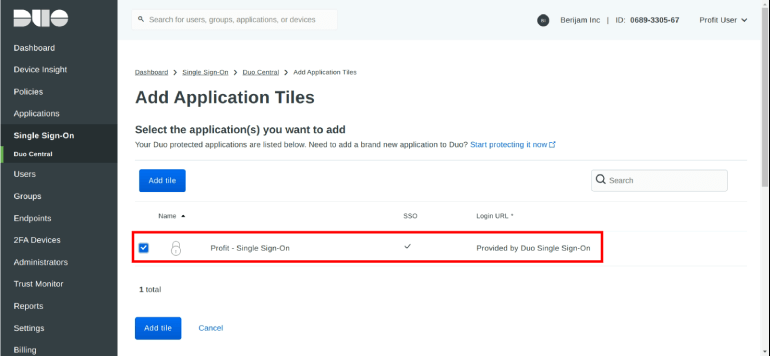
Step 10:
Select the Profit.co-Single Sign On in Application Tile page and click on Add Tile button.
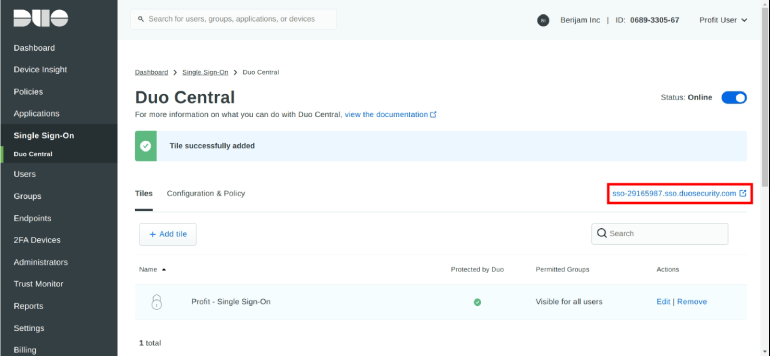
Step 11:
Click on the Duo Central subdomain URL it navigates to the Duo Central Application page.
Step 12:
In the Duo Central application page, click on the Profit.co-Single Sign On application and it redirects to the Profit.co account.

Step 13:
Click on the Profit-Single Sign On app, it redirects to the Profit.co account.